Description; Inappropriate granting of user rights can provide system, administrative, and other high level capabilities. The 'Generate security audits' user right specifies users and processes that can generate Security Log audit records, which must only be the system service accounts defined.
Openssl generate 4096 bit key. You can do this by using one of the following methods:.OpenSSLThe following sections describe how to use OpenSSL to generate a CSR for a single host name. Last updated on: 2019-12-20. Authored by: Stephanie FillmonBefore you can install a, you must first generate a certificate signing request (CSR).
Internet download manager key free. Applies to
- Windows 10
This reference for IT professionals provides information about the advanced audit policy settings that are available in Windows and the audit events that they generate.
The security audit policy settings under Security SettingsAdvanced Audit Policy Configuration can help your organization audit compliance with important business-related and security-related rules by tracking precisely defined activities, such as:
- A group administrator has modified settings or data on servers that contain finance information.
- An employee within a defined group has accessed an important file.
- The correct system access control list (SACL) is applied to every file and folder or registry key on a computer or file share as a verifiable safeguard against undetected access.
You can access these audit policy settings through the Local Security Policy snap-in (secpol.msc) on the local computer or by using Group Policy.
These advanced audit policy settings allow you to select only the behaviors that you want to monitor. You can exclude audit results for behaviors that are of little or no concern to you, or behaviors that create an excessive number of log entries. In addition, because security audit policies can be applied by using domain Group Policy Objects, audit policy settings can be modified, tested, and deployed to selected users and groups with relative simplicity.Audit policy settings under Security SettingsAdvanced Audit Policy Configuration are available in the following categories:
Account Logon
Configuring policy settings in this category can help you document attempts to authenticate account data on a domain controller or on a local Security Accounts Manager (SAM). Unlike Logon and Logoff policy settings and events, which track attempts to access a particular computer, settings and events in this category focus on the account database that is used. This category includes the following subcategories:
Account Management
The security audit policy settings in this category can be used to monitor changes to user and computer accounts and groups. This category includes the following subcategories:
Detailed Tracking
Detailed Tracking security policy settings and audit events can be used to monitor the activities of individual applications and users on that computer, and to understand how a computer is being used. This category includes the following subcategories:
DS Access
DS Access security audit policy settings provide a detailed audit trail of attempts to access and modify objects in Active Directory Domain Services (AD DS). These audit events are logged only on domain controllers. This category includes the following subcategories:
Logon/Logoff
Logon/Logoff security policy settings and audit events allow you to track attempts to log on to a computer interactively or over a network. These events are particularly useful for tracking user activity and identifying potential attacks on network resources. This category includes the following subcategories:
Generate Security Audits Registry Key Windows 10
Object Access
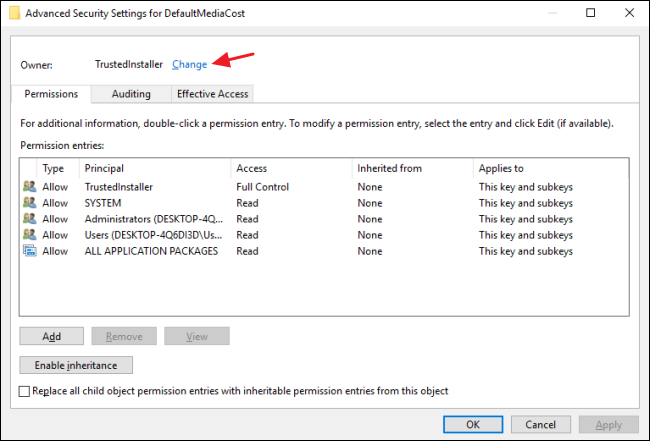
Object Access policy settings and audit events allow you to track attempts to access specific objects or types of objects on a network or computer. To audit attempts to access a file, directory, registry key, or any other object, you must enable the appropriate Object Access auditing subcategory for success and/or failure events. For example, the file system subcategory needs to be enabled to audit file operations, and the Registry subcategory needs to be enabled to audit registry accesses.
Proving that these audit policies are in effect to an external auditor is more difficult. There is no easy way to verify that the proper SACLs are set on all inherited objects. To address this issue, see Global Object Access Auditing.
This category includes the following subcategories:
Audit Registry Changes
Policy Change
Policy Change audit events allow you to track changes to important security policies on a local system or network. Because policies are typically established by administrators to help secure network resources, monitoring changes or attempts to change these policies can be an important aspect of security management for a network. This category includes the following subcategories:
Privilege Use
Permissions on a network are granted for users or computers to complete defined tasks. Privilege Use security policy settings and audit events allow you to track the use of certain permissions on one or more systems. This category includes the following subcategories:
System
System security policy settings and audit events allow you to track system-level changes to a computer that are not included in other categories and that have potential security implications. This category includes the following subcategories:
Physical Security Audits
Global Object Access Auditing
Global Object Access Auditing policy settings allow administrators to define computer system access control lists (SACLs) per object type for the file system or for the registry. The specified SACL is then automatically applied to every object of that type.Auditors will be able to prove that every resource in the system is protected by an audit policy by viewing the contents of the Global Object Access Auditing policy settings. For example, if auditors see a policy setting called 'Track all changes made by group administrators,' they know that this policy is in effect.
Resource SACLs are also useful for diagnostic scenarios. For example, setting the Global Object Access Auditing policy to log all the activity for a specific user and enabling the policy to track 'Access denied' events for the file system or registry can help administrators quickly identify which object in a system is denying a user access.
Note: If a file or folder SACL and a Global Object Access Auditing policy setting (or a single registry setting SACL and a Global Object Access Auditing policy setting) are configured on a computer, the effective SACL is derived from combining the file or folder SACL and the Global ObjectAccess Auditing policy. This means that an audit event is generated if an activity matches the file or folder SACL or the Global Object Access Auditing policy.
This category includes the following subcategories:
Edit user account privileges.
This utility does work under all recent versions of Windows, although (like all Resource Kit tools) it is unsupported.
Below are the Privileges that can be granted or revoked, all are Case-Sensitive.
Logon Privileges:
System Admin Privileges:
Service Privileges:
Misc Privileges:
The Se_Deny… rights will override the corresponding account rights.
An Se_Deny… right will override any logon rights that an account may inherit as a result of its group membership(s).
To run NTRIGHTS you need to be an administrator.
To change privileges remotely (-m option) you need to have administrator rights on the machine being changed.
It is often helpful to grant the privileges to a named group, e.g. grant SeServiceLogonRight to a group called ServiceAccounts, then add individual user accounts to that group.
The group policy editor can be used to view these privileges in a GUI.
On a Windows 2008 Server (or Vista), allowing logon through Terminal Services (SeRemoteInteractiveLogonRight) requires an extra step: Control Panel > System > 'Remote Settings' > 'Select Users' button, and then add users/groups.
Generate Security Audits Registry Key Free
Examples:
Allow all members of the local 'Users' group to logon locally:
ntrights -u Users +r SeInteractiveLogonRight
Allow members of the domain group 'Admin-RDP' to logon remotely via RDP to 'server64', also log this security change in the event log:
ntrights -u ss64DomAdmin-RDP +r SeRemoteInteractiveLogonRight -m server64 -e 'Added RDP rights for Admin-RDP'
Allow the domain user 'Ashley' the right to run a batch (Scheduled Task) on Server64:
ntrights -u ss64DomAshley +r SeBatchLogonRight -m server64
Network Security Audits
Allow all members of the domain group 'Admin-Local' to shutdown this computer:
ntrights -u ss64DomAdmin-Local +r SeShutdownPrivilege
Allow the domain user 'JDoe' to shutdown the machine 'Server64' :
ntrights -u ss64DomJDoe +r SeShutdownPrivilege -m Server64
Penetration Testing
Allow any Interactive user of the local machine the right to change the system time:
ntrights -u INTERACTIVE +r SeSystemtimePrivilege
Specifically deny local logon rights to Henry:
ntrights -u Henry +r SeDenyInteractiveLogonRight
“What distinguishes the majority of men from the few is their inability to act according to their beliefs” ~ Henry Miller
Related:
UserRights.psm1 - PowerShell module to grant, revoke, and query user rights (privileges).
CACLS - Change file permissions.
Q315276 - Set Logon User Rights by Using the NTRights.
Logon Types - Windows Logon types.
Technet - User Rights and Privileges.
Some rights reserved